SECURE PASSWORD AUTHENTICATION APPLIANCE
Password Protect solves the problem of bulk identity theft by replacing your existing password database, that is vulnerable to attack by hackers, with an impenetrable hardware authentication appliance.
Login credentials including usernames, passwords, PINs and answers to secret questions received by your service are sent to a Password Protect appliance for validation.
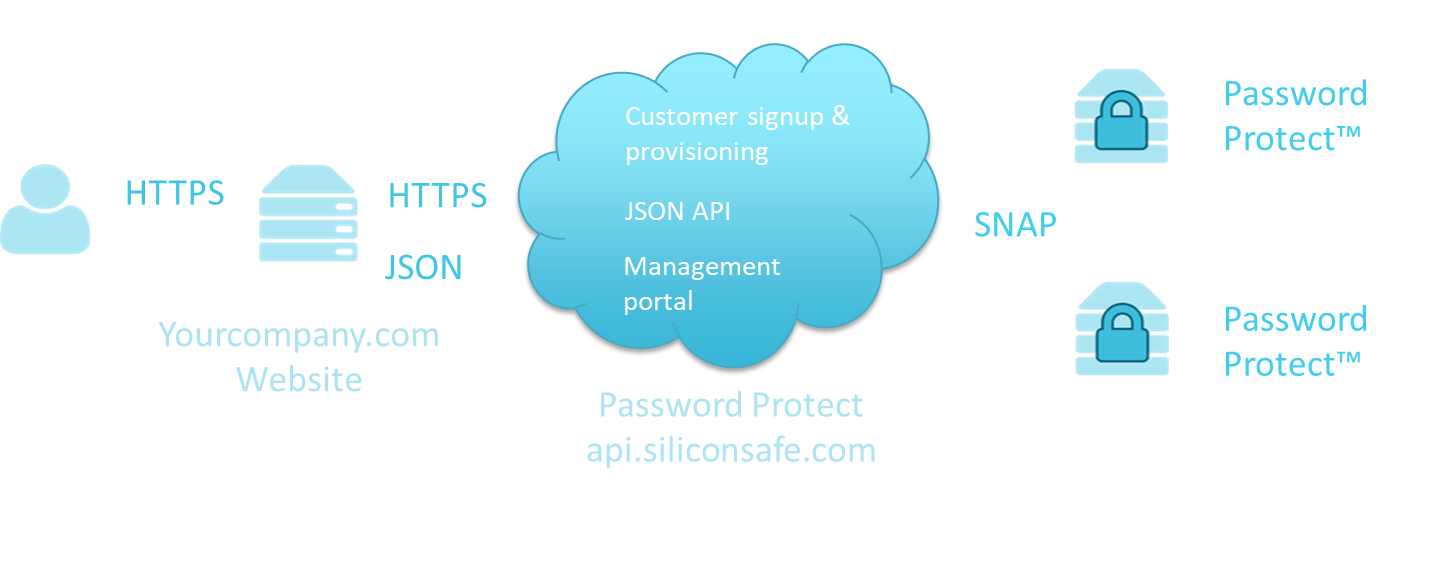
The solution is available as a multi-tenant hosted managed service with the appliances physically located in our group’s own data centers in Europe, America and Asia-Pacific. Each tenant has their own secure namespace. By having separate namespaces, different tenants can store the same usernames without interference.
EASY INTEGRATION
Integration with your existing authentication code is straightforward. Instead of validating identities and passwords using a SQL query to a database in your network, you send the credentials to the Password Protect cloud service for validation using an HTTPS Post. Our migration tools make light work of moving existing credentials into Password Protect, without the need to reset passwords.
SECURE AND RELIABLE
Each Password Protect authentication appliance can store millions of login credentials and authenticate thousands of users per minute. Appliances have disaster recovery and high availability features built in, and are clustered for scalability, load balancing and failover including geographical redundancy.
OUR SOLUTION: PASSWORD PROTECT™
No-Read™ Authentication Appliance
With Password Protect we have developed an impenetrable password storage and authentication appliance. It is based on our radical new patented No-Read™ platform, and prevents data theft by adopting the following protection strategies:
No-Read – You set a password against a username and can verify those two credentials together, but you cannot read a password, username, PIN or answer to a secret questions out of the Password Protect appliance. Only verification results leave the device over a network connection, never the data itself. There are no back-doors and no administrator password overrides over a network connection.
No-Malware – Password Protect does not execute external programs. This makes it immune to all types of malware infection, buffer overflow attacks, cross-site scripting attacks and SQL injection attacks. In fact any code injection attack is impossible.
No-PC or OS – Password Protect is not a PC and doesn’t run an operating system, database or conventional software stack. This reduces the ‘attack surface’ and provides immunity against thousands of vulnerabilities associated with the PC platform. Neither does Password Protect rely on encryption and user privileges to keep data safe.
In order to do this Silicon:SAFE has gone beyond the use of cryptographic and operating system based solutions and developed a hardware repository, a no-read appliance that physically encapsulates password data. Once password data is entered into the appliance, it cannot be read out again during a cyber-attack.
You can think of the Password Protect appliance as the hardware implementation of principles behind the use of hashing and shadow files. Once password data is created then it never needs to be read again. But instead it is used as reference data to compare against password ‘guesses’. Passwords include PINs and answers to secret questions. Future product iterations will include Biometric passwords such as finger print images and retina scan images.
The Password Protect appliance stores username/password pairs so that once a pair is registered in the hardware it is impossible to read the password out from the hardware by remote access. To verify that a user has a particular password you must ask the hardware to test a username/password pair against what is stored and the hardware will return a YES or NO answer. With no interface for the hardware to divulge passwords, you cannot ask the hardware what a password is for “Customer X”, or request a dump of the password file. So, if you want to get the password file out of the hardware you have to physically interact with the box.
This raises an important question: how is backup performed if you can’t get the passwords out of the appliance? The solution is to replicate changes between appliances. When a username/password pair is added or changed to one appliance it immediately replicates the changes to other ‘backup’ appliances on a private network link. As a consequence of this approach there is no need for a bulk transfer of passwords between appliances, nor is it necessary or possible to dump the password repository to backup media over the internet where it is vulnerable to theft.
The solution is to store data directly in the silicon. So Password Protect does not rely on passwords being hashed or encrypted. Nor does it utilize an operating system that can be flawed by vulnerabilities, and it does not rely on a key management system. It is immune to social engineering attacks over the internet because there are no administrator passwords or other mechanism susceptible to human error which can result in the extractions of credentials.

SOLVING THE PROBLEM OF BULK IDENTITY THEFT
Because you cannot read credentials from Password Protect or re-program it with malware to implement a backdoor read interface, it’s impossible to steal login credentials from a Password Protect appliance during a cyber-attack, eradicating the menace of bulk password theft over the internet.
If companies such as Adobe, eBay, Yahoo or Ashley Madison had used Password Protect, then data breaches comprising millions of login credentials could not have happened.